Hi All,
Just a few Hours ago, Microsoft has released the MicrosoftTeams PowerShell Module 5.
Hi All,
I’ve tried to register a Yubikey 5 NFC with my Android OnePlus9 (has Android 13 installed).
Hi All,
VMware has released a Security Advisory for VMware Tools
Hi All,
I’ve had a warning in my Azure DevOps Pipeline, that deploys this Blog via Hugo to Azure Static Website.
Hi All,
Today i’ve seen the notification, that Azure Storage Explorer 1.

Hi All,
In Microsoft Code 1.79, there has been an update that fixes a security issue.

Hi All,
Yesterday, Microsoft has released new Exchange Security Updates. Read more at the Blog Post from the Exchange Team

Hi All,
Lately KeePass was in the Press because of the Security Eploit below.
Hi All,
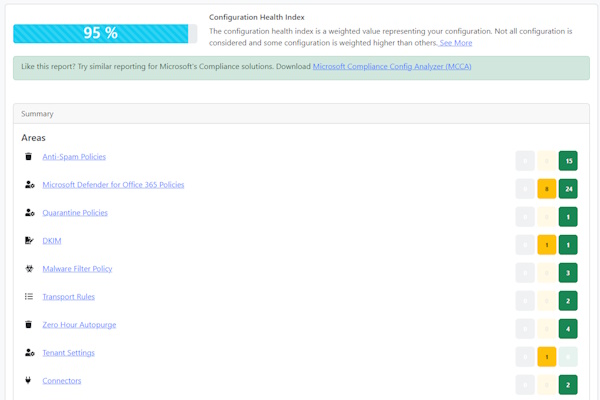
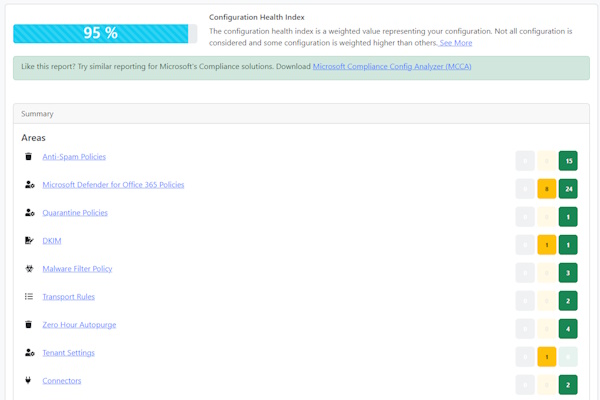
Just a few Hours ago, the Microsoft Defender for Office 365 Recommended Configuration Analyzer (ORCA) 2.

Hi All,
In 2015 i wanted to know how many SMTP Servers used STARTTLS, SPF, DKIM, DMARC.